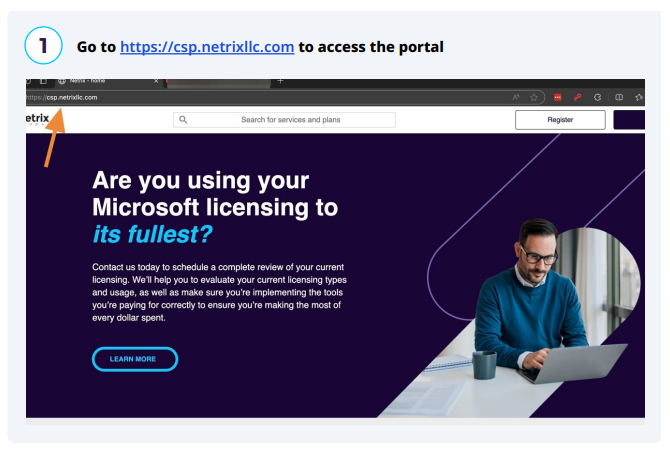
Service Portal Upgrade Notice
DOCUMENTATION On June 1, if you attempt to log into the Employee Service Center using your existing URL, you will see a notice informing you that the portal has been upgraded and directing you to log in to the Business Portal instead. Please use the link above to access the new portal